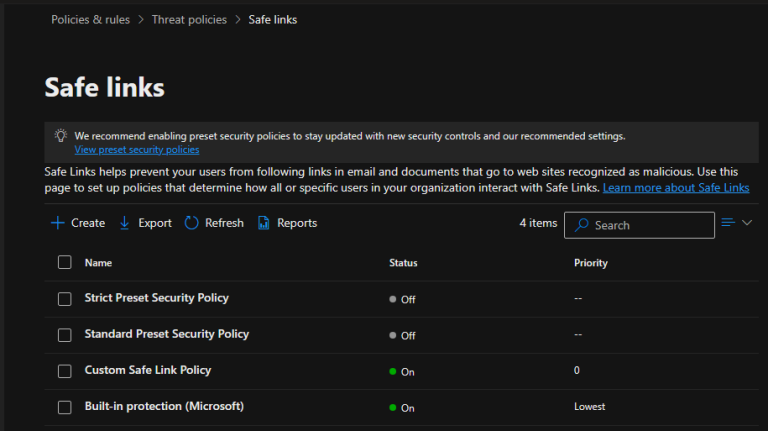
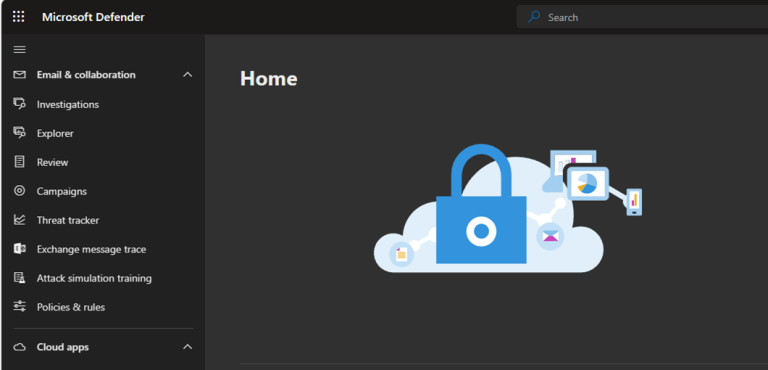
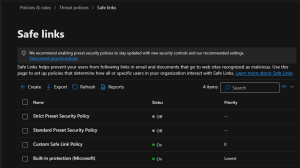
Safe Links is a feature in Microsoft Defender for Office 365 (formerly known as...
FULL BLOG
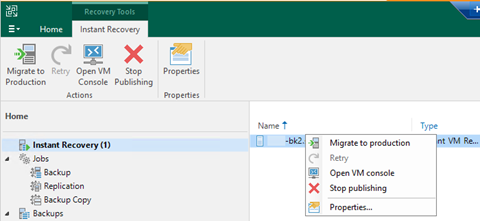
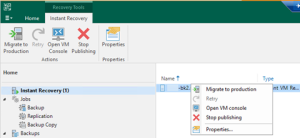
Let's walk through the steps to perform a Physical to Virtual machine (P2V) conversion...
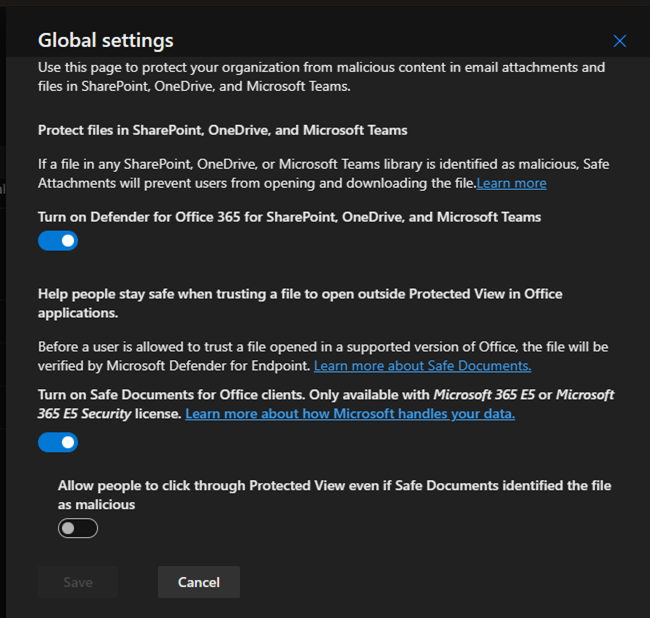
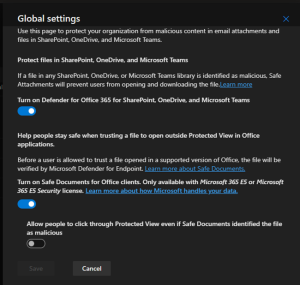
In Microsoft Defender for Office 365, Safe Attachments is a feature that helps protect...
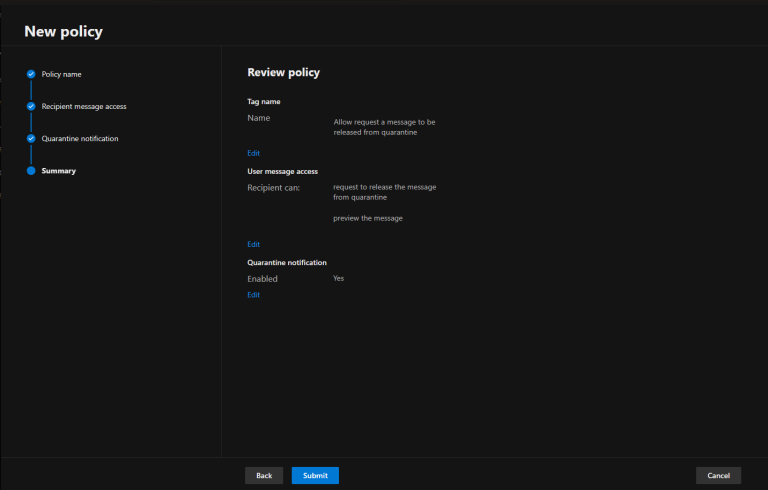
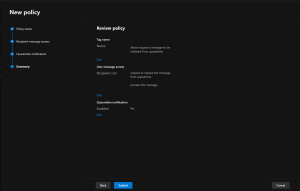
Creating a custom quarantine policy in Microsoft Defender for Office 365 involves configuring advanced...
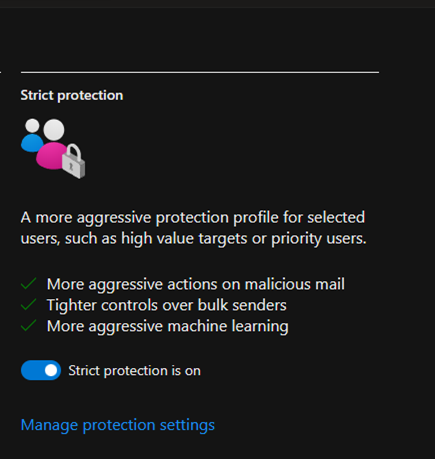
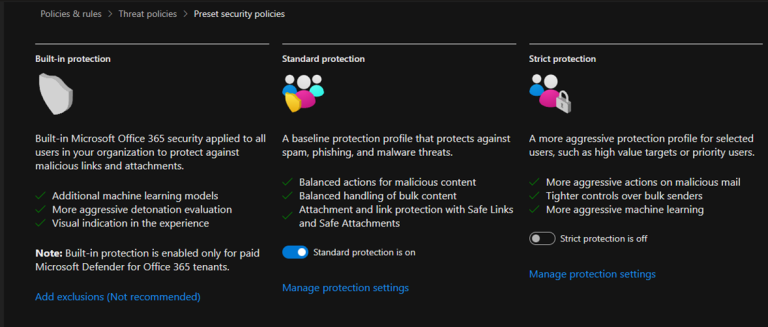
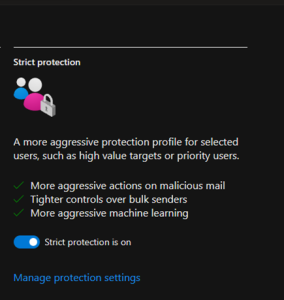
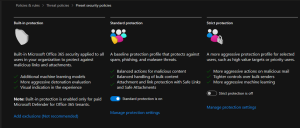
Strict preset security policies typically refer to predefined rules and guidelines designed to enhance...
Microsoft Defender for Office 365 provides preset security policies to help organizations protect their...
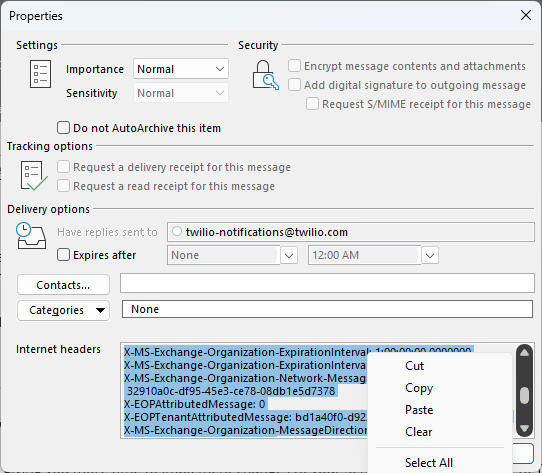
Authenticated Received Chain (ARC) is a mechanism used in email authentication protocols to address...
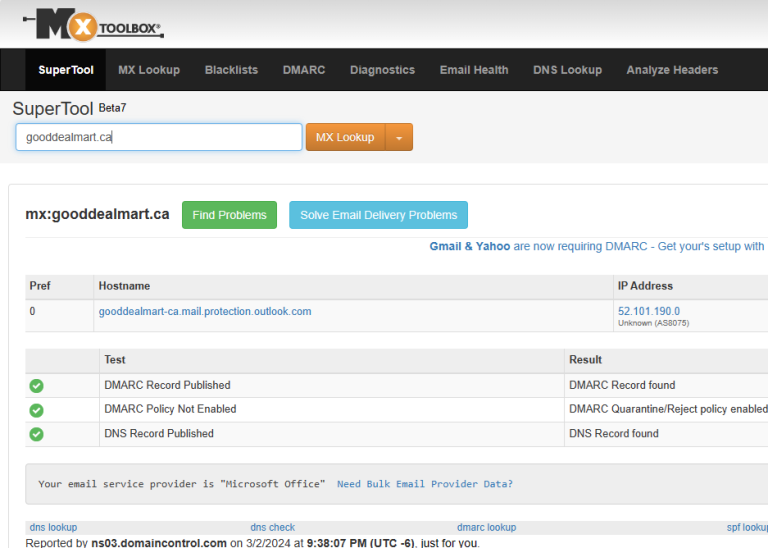
Domain-based Message Authentication, Reporting, and Conformance (DMARC) builds upon SPF and DKIM to give...
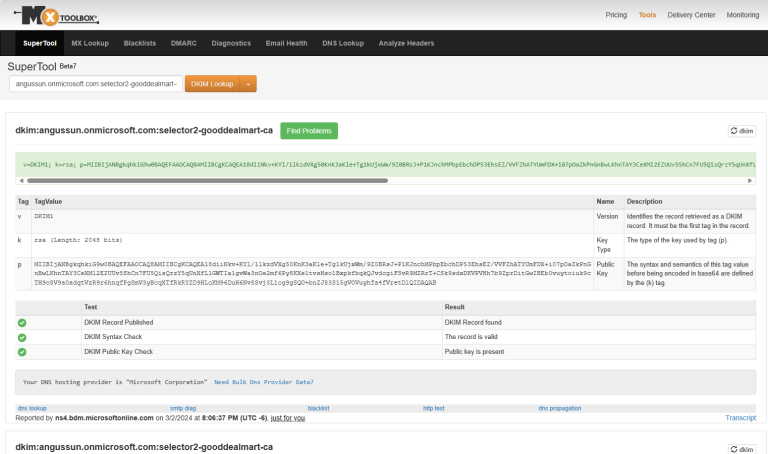
DomainKeys Identified Mail (DKIM) allows email senders to sign their outgoing emails digitally using...
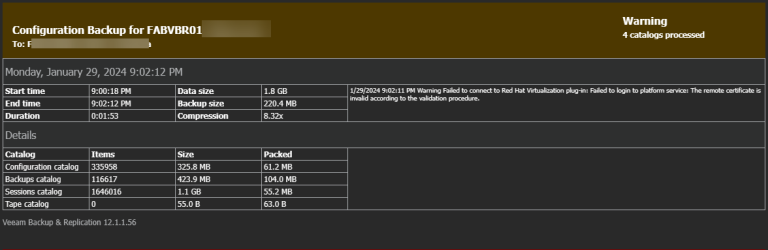
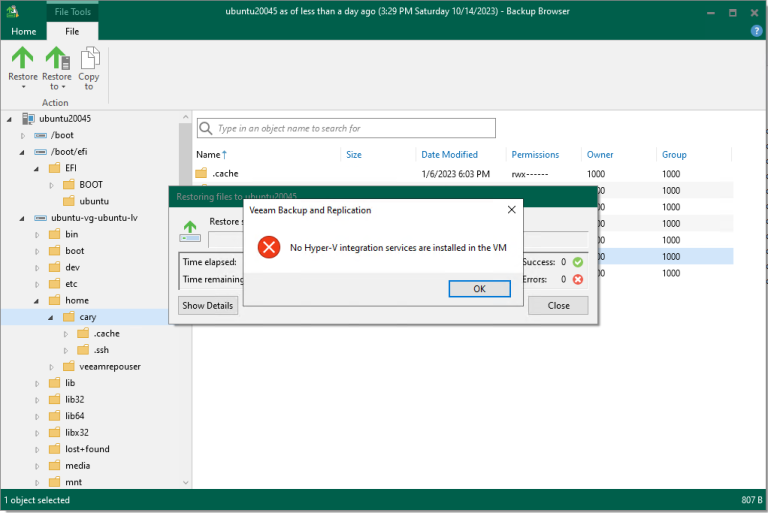
This is a very interesting warning. I migrated many VBR servers, and it's the...
Cisco Security Advisory was released today about the Cisco Unity Connection Unauthenticated Arbitrary File...
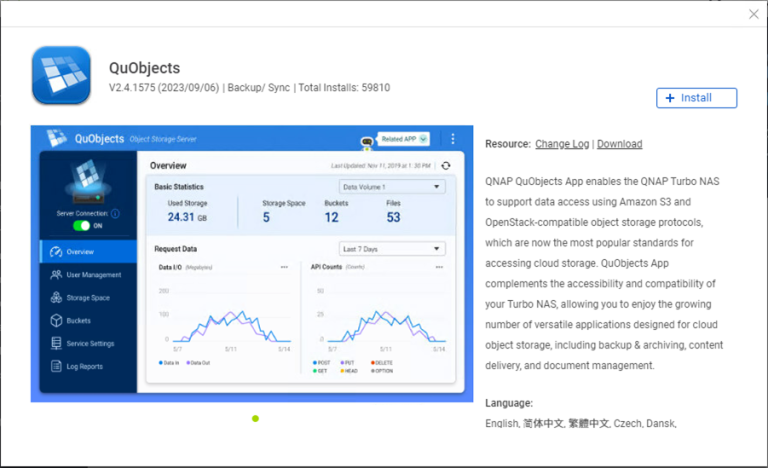
QNAP QuObjects application is free and certificated for objects with immutability, which means you...
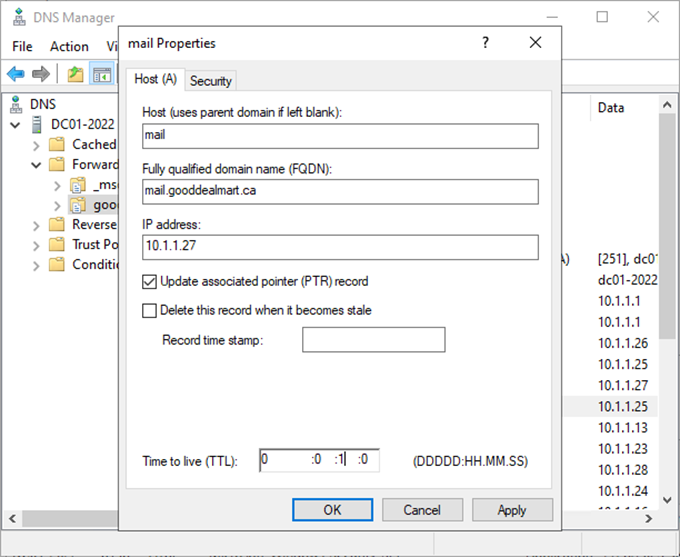
To transition the client access namespace to Exchange Server 2019, change the DNS record...
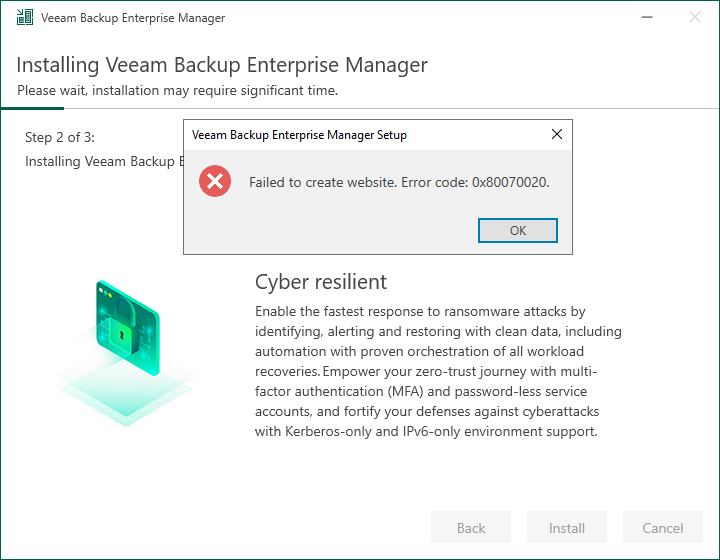
When you try to install or upgrade the Veeam Backup Enterprise Manager 12.1, it...
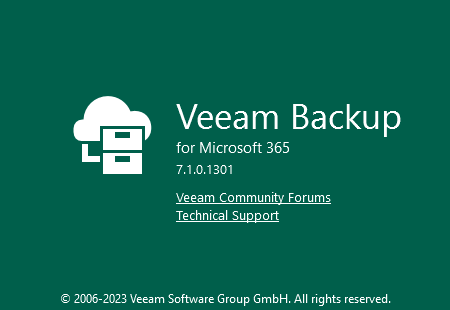
Veeam released the version of Veeam Backup for Microsoft 7a on December 5, 2023....
Veeam Backup Enterprise Manager is a centralized management and reporting tool designed by Veeam...
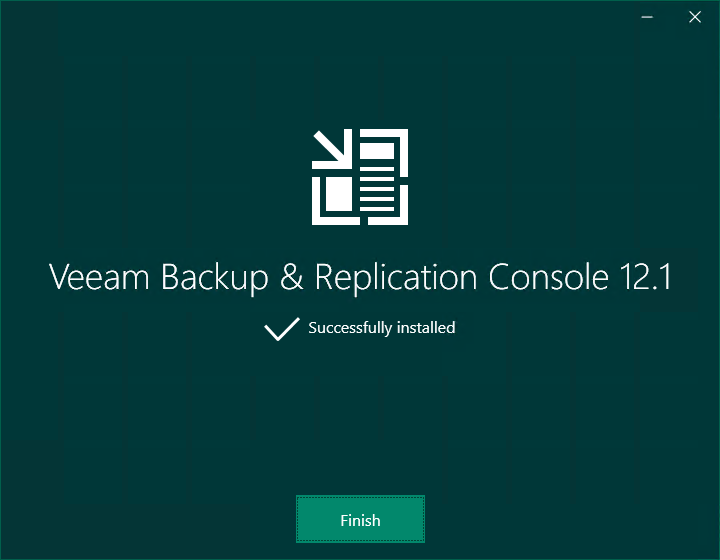
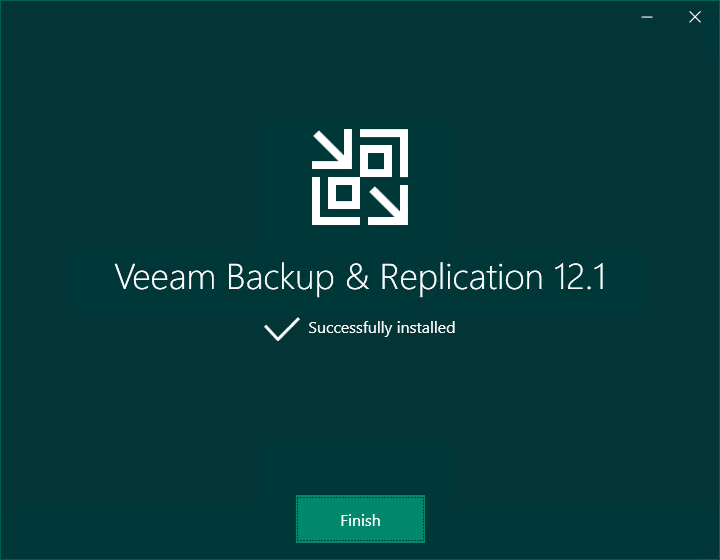
When you install Veeam Backup & Replication v12.1, the Veeam Backup & Replication console...
When you install Veeam Backup & Replication v12.1, the Veeam Backup & Replication console...
Today, I will show you how to install Hyper-V integration services in the Ubuntu...