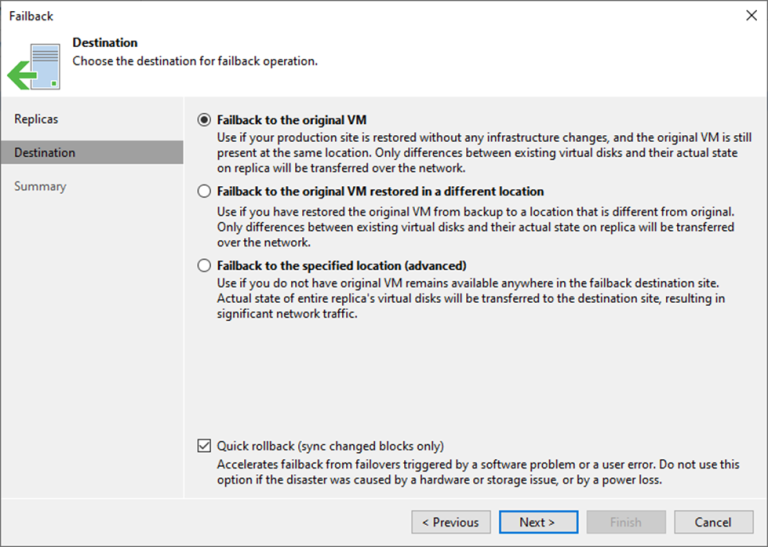
Failback is returning operations to the primary site after a disaster recovery event. It...
FULL BLOG
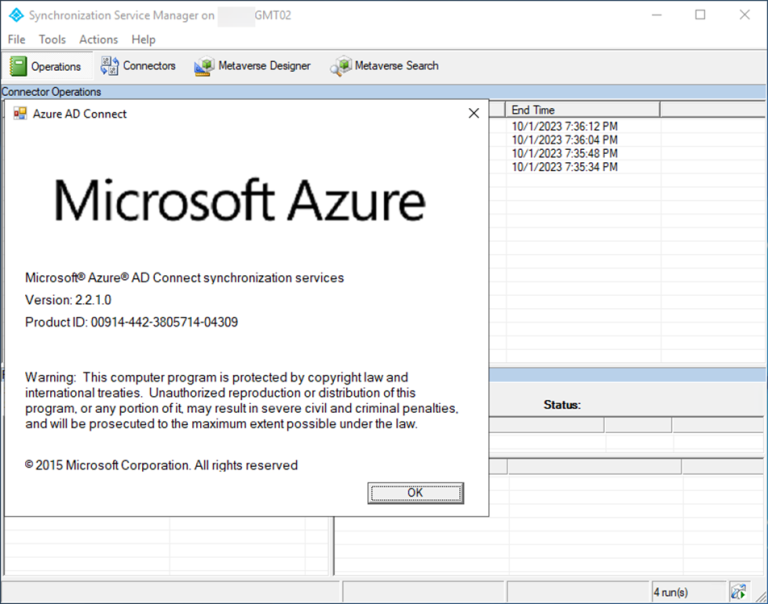
Today, I will show you how to migrate Microsoft Entra Connect (Azure AD Connect)...
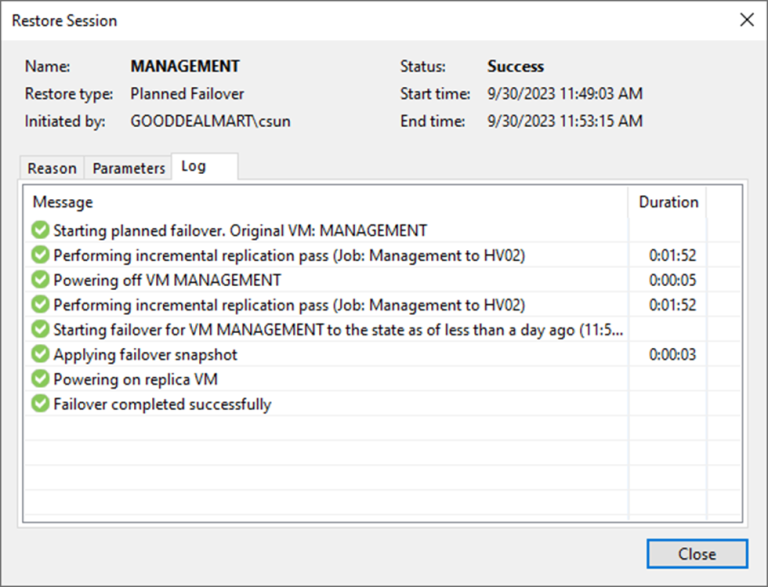
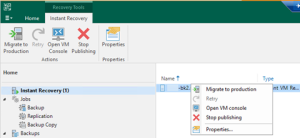
Planned failover is the smooth manual switching from a primary VM to its replica...
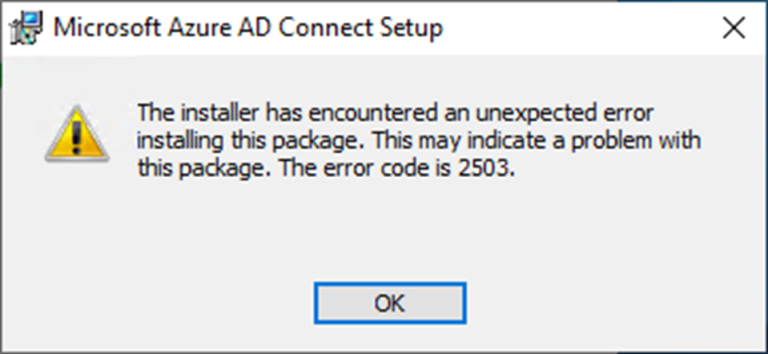
When you try to install the Microsoft Entra Connect V2 (Azure AD Connect V2)...
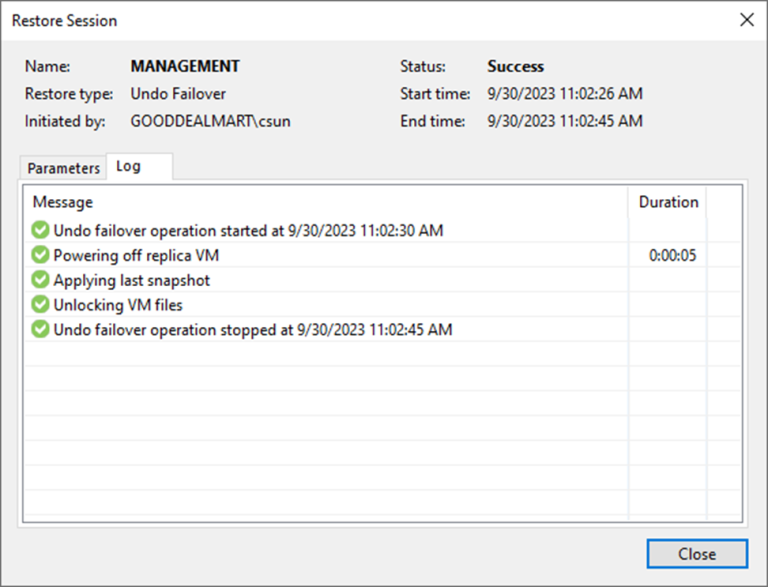
One method for completing failover is to use failover undo. When you undo failover,...
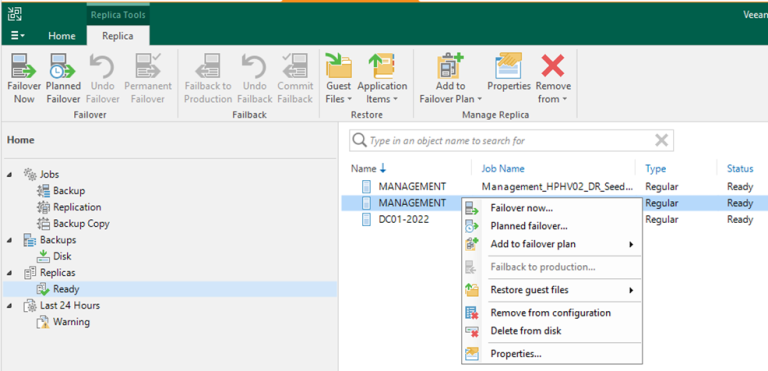
Failing over a virtual machine to a disaster recovery site involves replicating the virtual...
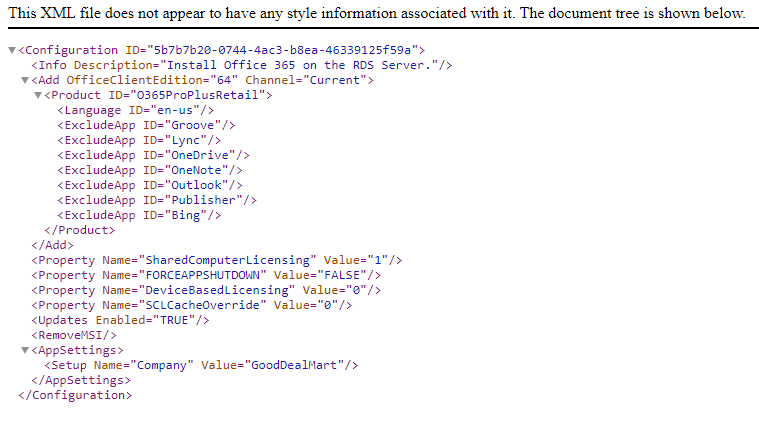
Microsoft 365 Apps are installed on a machine is set up as a Remote...
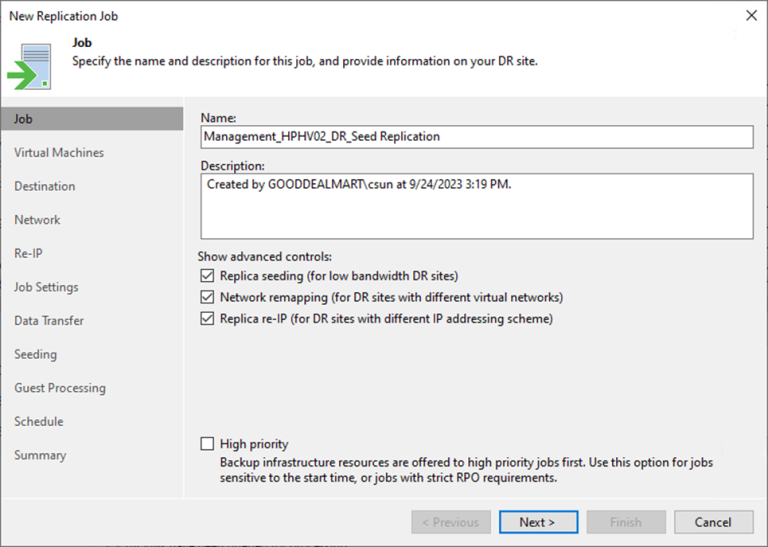
This procedure creates a replication job with seeding to replicate the specified VMs to...
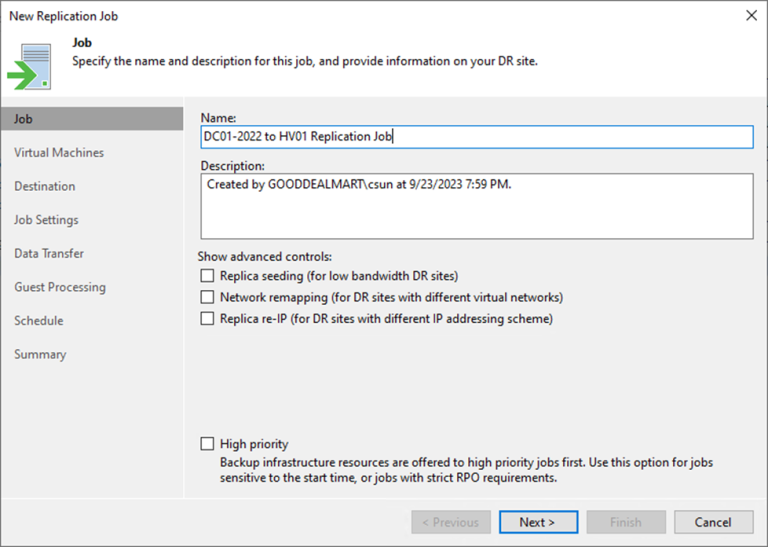
This procedure creates a replication job to replicate the specified VMs to the disaster...
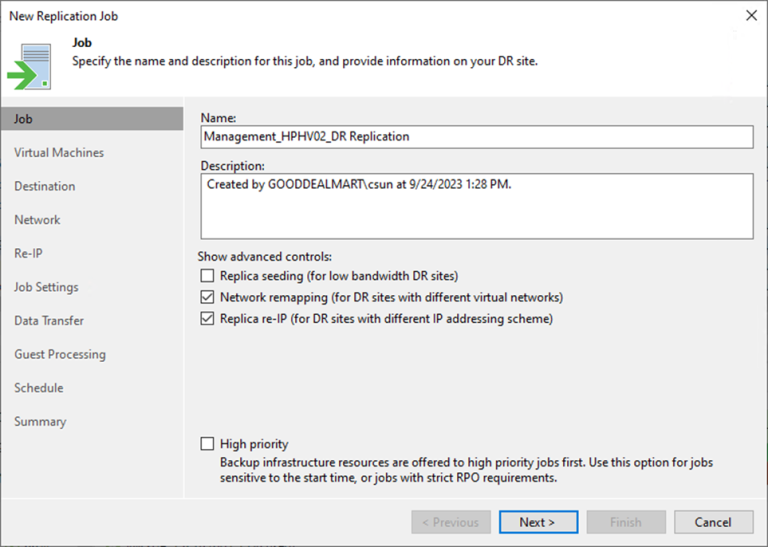
This procedure creates a replication job to replicate the specified production virtual machines at...
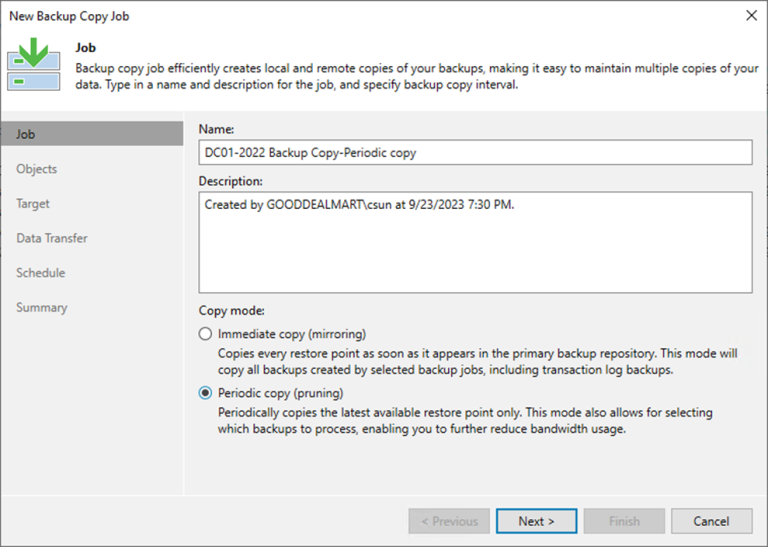
Periodic copy jobs can be scheduled to run during non-business hours or low-activity periods,...
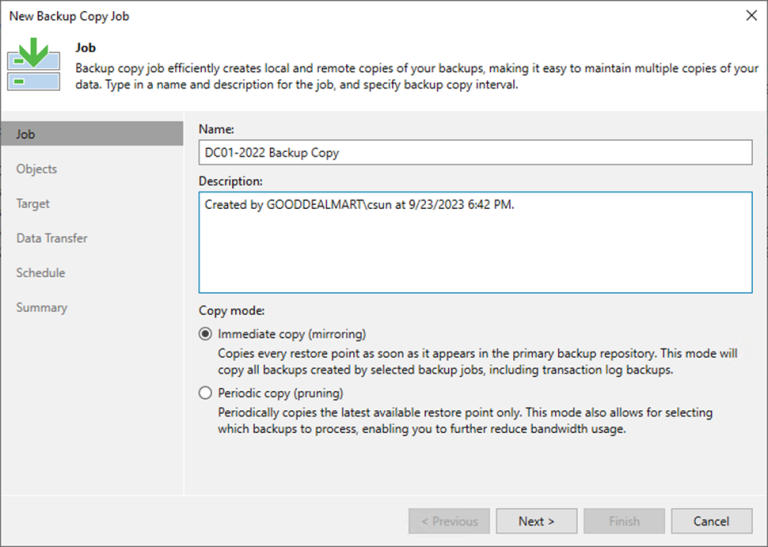
Immediate copies help reduce your RPO, which is the maximum allowable data loss in...
This process creates a backup job to backup the VMS of the Hyper-V host...
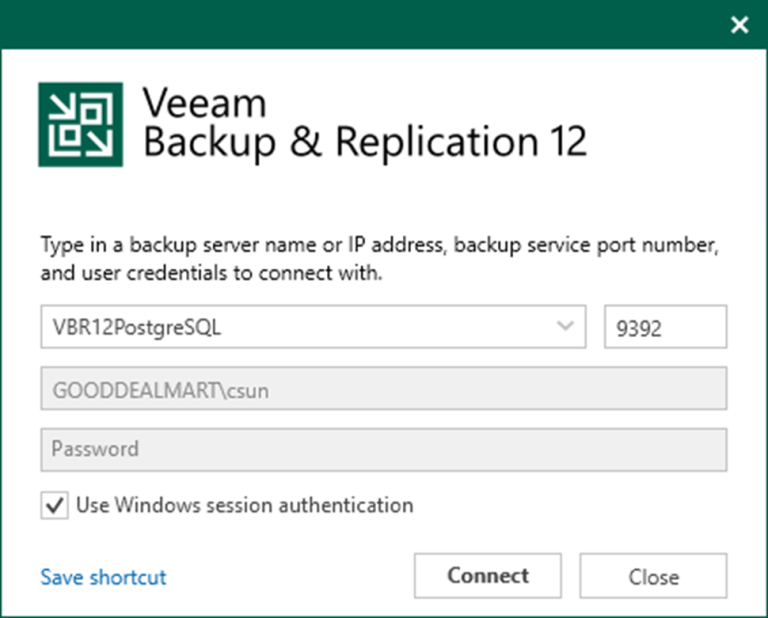
You also need to install Cumulative Patches P20230718 for Veeam Backup & Replication Console...
Veeam Backup & Replication 12 cumulative patch P20230718 was released on March 07, 2023,...
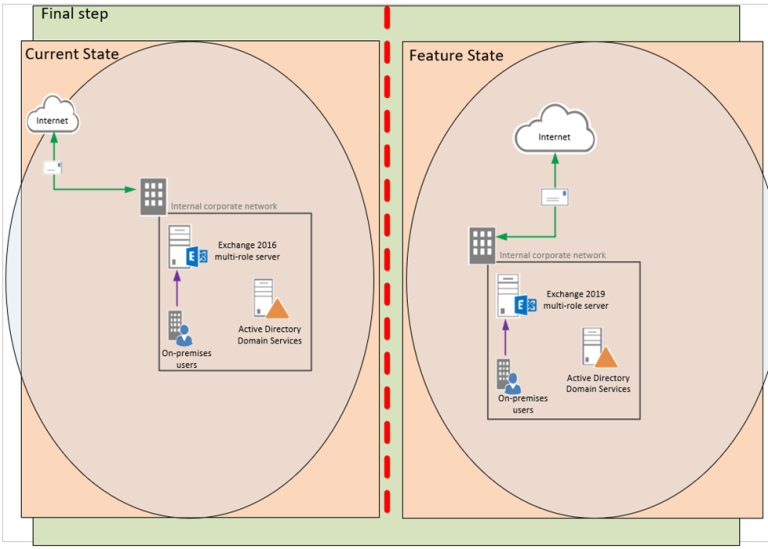
Deploying Exchange Server 2019 involves several steps, including preparing the Active Directory environment, installing...
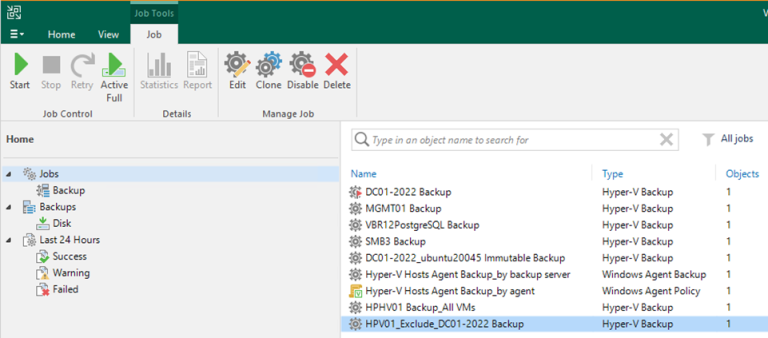
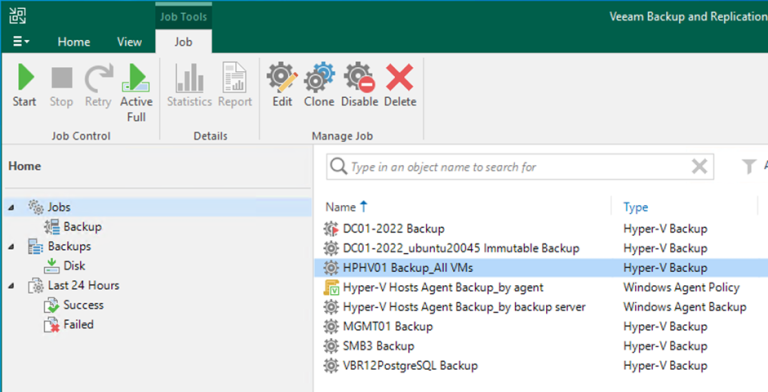
How to create a Backup job to backup all VMS of the Hyper-V Host at Veeam Backup and Replication v12
This procedure creates a backup job to back up all VMS of the production...
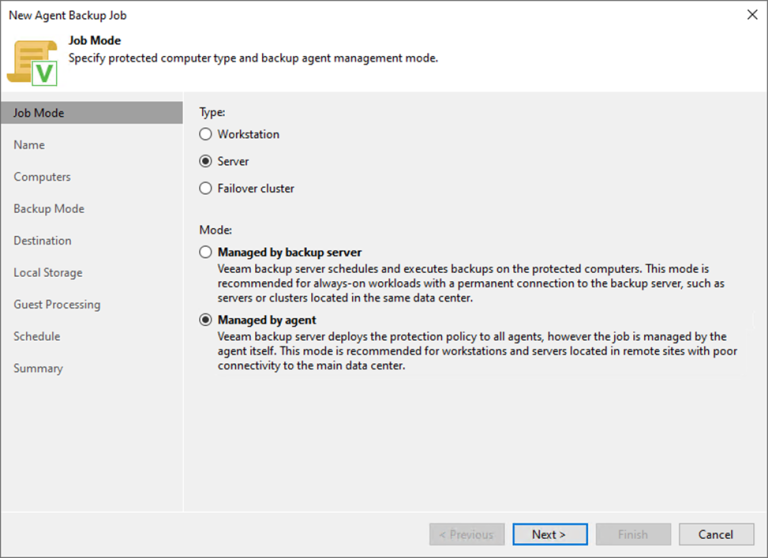
This procedure uses the managed by agent mode to create a backup job to...
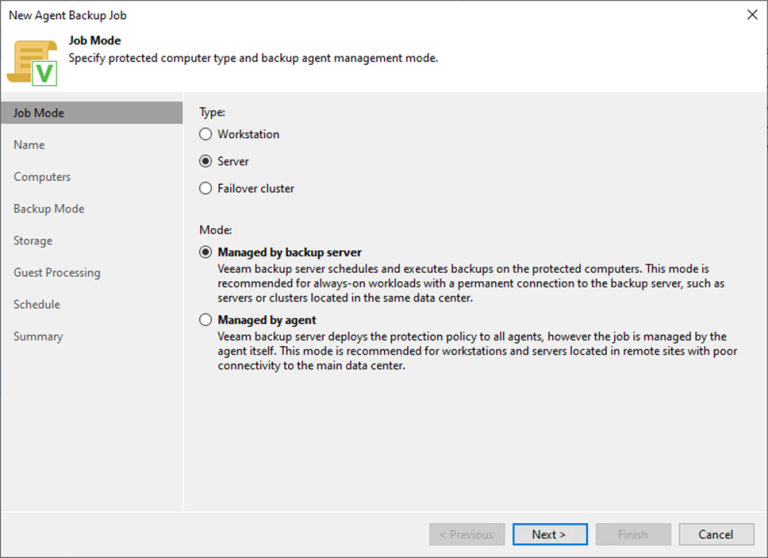
This procedure uses the managed backup server mode to create a backup job to...
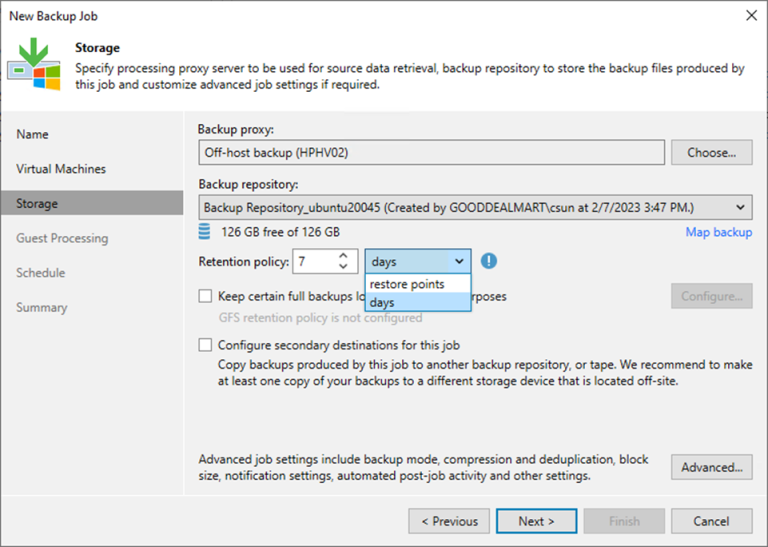
Immutable Backup is a Veeam Backup & Replication feature that protects against ransomware attacks...